Well, I guess it had to happen at some time.
To be fair, I was parked on double yellow lines. No excuses, no basis to contest the penalty... I was in the wrong.
In those 10 minutes however, I unwittingly caused Walsall Metropolitan Borough Council sufficient financial hardship to warrant a £70 fine; reduced to £35 if I paid within 14 days. In a cleansing act of contrition, I paid via the "secure online payment system".
What's wrong?
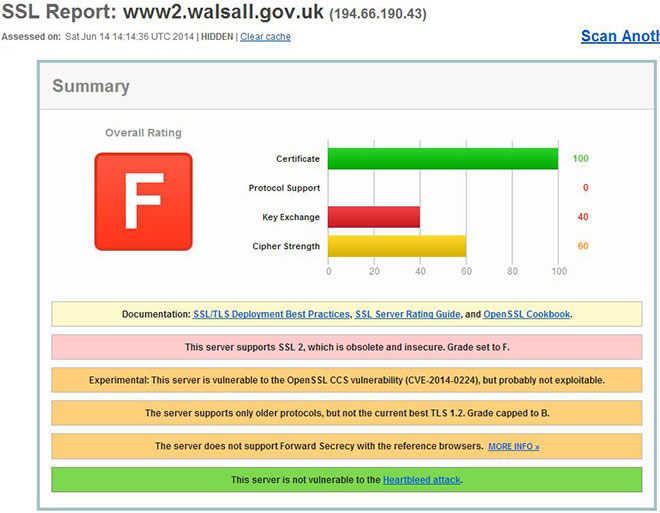
Your private, confidential payment details are being leaked over insecure protocols. These insecurities mean Walsall MBC are breaching PCI regulations each and every time they take a payment online.
What is PCI?
The Payment Card Industry Data Security Standard (PCI DSS) is a set of requirements designed to ensure that ALL companies that process, store or transmit credit/debit card information maintain a secure environment.What have they done about it?
I notified Mrs Samantha Price from their I.T team on June 2nd 2014. To my amazement, they had literally just completed their annual audit and it had been signed off as "secure". When I questioned how the process was handled, she said:"It's a Government Gateway service, so we just ask them if it's compliant."
Quite a rigorous process then! I agreed to forward some detailed information to her; I was expecting a response fairly quickly... given the nature of the issue. 3 days later, nothing. When I called for an update, I discovered Mrs Price had gone on annual leave and passed it to Mrs Emma Tate in the Communications department. Unfortunately, while trying to transfer my call and while still believing I was on hold, Mrs Tate accidentally relayed their internal dialogue.
"It's that bloke off Twitter" and "Sam emailed me this, saying she doesn't really understand it"
Run that by me again?! The I.T Team Leader doesn't understand PCI compliance? Jeez!
When she realised her mistake, she promptly cut me off. Charmin'
I escalated it with the Chief Executive on June 4th 2014. Thus far, nothing has changed. No explanation and no mitigative action whatsoever! If you've made a payment since June 2nd, I'd like to hear from you.
Are they subject to any penalties?
I reported the issues to VISA, MasterCard & the Information Commissioner's Office.Mastercard can (and often do) issue fines of $25,000 for each breach. VISA on the other hand, issue $25,000 a month fines for as long as the breach continues. The Information Commissioner's Office have the necessary powers to impose a £500,000 fine - but I doubt they'll even get involved. Trouble is, the ICO aren't interested in (and often don't understand) the technical aspects of a breach; focussing instead on accountability and if the Council have taken the necessary action, regardless of how effective it is.
I have also started legal proceedings against Walsall MBC. I can't provide further details at this time, but I will update this article as & when necessary.
If this goes unnoticed with one Council, how many others are vulnerable?
Wider Research (can open, worms everywhere!)
I Google'd "Pay PCN" and tested 32 councils, literally as they appeared in the search results. The following may appear to be cherry-picked, but I assure you, they're not.Of the 32 council sites I tested until the vein in my head burst, a whopping 23 were found to be processing payments in breach of PCI, PECR and DPA regulations.
Who passed PCI Compliance?
Traffic For London (TfL) Birmingham City Council Chelmsford City Council Wolverhampton City Council Royal Borough of Kensington & Chelsea Leicester City Council Coventy City Council The Royal Borough of Kingston upon Thames Counciland finally, with one of the finest implementations...
Canterbury City Council
Someone at Canterbury City Council has made a real effort to provide solid SSL/TLS to their users and deserve to be acknowledged.
Who failed PCI Compliance?
[print_gllr id=1227]The two worst offenders... North Tyneside Council & the London Borough of Bexley; both managing to not only make a hash of security, but the latter have forgotten to renew the certificate which expired on June 2nd 2014.
Bear in mind, I uncovered these in under 30 minutes of searching Google. What do the auditors and the ICO actually do on a daily basis? It's also worth noting... there's more to PCI compliance than a solid SSL/TLS installation. Just because it passes online doesn't necessarily mean their internal processes are secure enough to be fully compliant.
Is it a lack of investment?
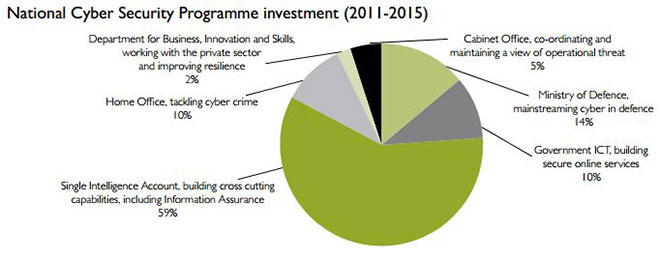
Since 2011, the Government has invested £650m on its Cyber Security Strategy, £65m of which has been spent on "building secure online services". They've recently added a further £210m to the pot too.
£650m on what the government describe as a "Tier 1" threat? Is that it? We're about to spend/waste another twenty BILLION on phase #2 of HS2!
That said, I don't believe funding is the issue. An extra few million isn't going to miraculously transform Mrs Price into the font of all knowledge regarding PCI. Conversely, a hefty fine from the ICO and/or members of the Security Standards Council isn't going to benefit the public either.
You can't put yourself out there as the representative model of best practice, only to repeatedly fail at even the most basic level. It's embarrassing, disgraceful and of detriment to firms to whom the phrase "security" means more than a check box on a form.
These aren't mistakes. It shows a fundamental lack of understanding and total disregard for data safety. In my opinion, those responsible should be shown the door; system administrators, auditors, the ICO and ultimately, the government for presiding over such incompetence.
Summary
Fines & penalties should work both ways. I breached parking regulations and duly paid the penalty. At least 23 Councils are breaching payment regulations and should be made to not only pay the appropriate fine, but compensate their "customers" directly for leaking data over protocols which became insecure & obsolete in 1996.If you believe you've been affected or have recently made an online payment to one of the aforementioned Councils, take appropriate action.
Visa Data Compromise Team: 0207 7955453 or [email protected]
Mastercard: [email protected]
If you know of any others, please let me know.
Don't forget to +1, RT and Like below.
