Ah, passwords. The thought of choosing, remembering and inevitably resetting them is enough to make your blood boil.
As a fundamental part of our digital lives and despite several reports claiming they're dead, our dependence on them shows little sign of slowing. A password manager is a great way to virtually eliminate the stress & hassle associated with passwords; itself sufficient reason to give them a whirl.
Pick a good one though, and you'll almost certainly be safer too.
![]()
What do they do?
The feature set varies from product to product, but minimally they...
- Generate new, strong & unique passwords for you. Re-using a password is the quickest way to undermine your security.
- Store those passwords in an encrypted manner, so they're safe from prying eyes.
- Remove the need to remember multiple passwords.
- Automate the process of entering usernames & passwords each time you login.
Many are able to fill out forms too, speeding up an otherwise laborious registration process.
1Password is my product of choice, for reasons you can read here: https://ramblingrant.co.uk/1password-forgot-your-password-youre-doing-it-wrong
How do they work?
During setup, you'll be asked to provide a "master" password. This is the only password you'll ever need to remember, so make it as long and strong as you possibly can. More on that later.
The master password forms the basis of a cryptographic key, which the application uses to encrypt your data. These aren't (or shouldn't be) stored anywhere, as doing so would weaken, if not completely undermine the encryption process. Think of it as buying a category 5, insurance-approved door lock... and leaving the key under the mat ;)
All 6 applications use a cryptographic algorithm called AES, or Advanced Encryption Standard. AES is a symmetric algorithm, meaning the same key is used to encrypt and subsequently decrypt your data. AES128/256 combined with a strong key & solid key management affords you immense security, such that a brute-force attack just isn't feasible.
This data is usually stored on your device, a USB drive or in the cloud.
What are the risks?
Let's look at the threat landscape and associated risks.
1. The application might not be secure in its own right.
The use of AES doesn't automatically mean it's secure. Before you buy, look for security reviews online.
2. Choosing a weak master password potentially places all passwords at risk.
Choosing a long, strong & unique (never used before!) master password is crucial. Before you make a decision, pick a password (do it now) and sit with it for a week. Every time you pick up your laptop or switch on your PC, see if you can remember it. If you use your devices daily, it'll quickly become second nature to you.
Don't think of your passwords as secure/not secure (without context, "secure" is meaningless), but how resilient they are to different attacks. Also, consider the value of the data you're trying to protect.
Tips for creating a strong password:
- Use 12 characters or more.
- Include upper/lowercase characters.
- Include special characters (!"£$%&*()_+<>:@~{} et al)
- Don't follow a pattern, be random! Obvious substitutions like $ for S or £ for E are exactly that; don't underestimate how resourceful an attacker can be.
- Don't use words. The average vocabulary for someone aged 35-50 is < 30,000 words. A password consisting of 3 entire words is very weak, regardless of length.
- Ignore advice from XKCD comic strips or the UK government.
3. Though nearly all apps lock automatically after a period of inactivity, leaving an unlocked session open can leak your credentials to anyone with access to the machine.
Never rely on the application to lock your account for you. If you have to leave your PC, lock it. It's quicker to enter your master password again than reset them all if you're compromised.
4. Anyone in possession of your master password can access everything.
This is the biggest threat to any password manager and a common stumbling block for anyone looking to adopt this methodology.
Let's get some perspective first.
Online PW Managers
Some applications provide web-based access to your passwords (LastPass, Roboform et al).
The firms behind these products store your encrypted passwords in the cloud, allowing you to access them from anywhere with an internet connection. All things being equal, there's no immediate risk in storing them in this manner. What matters, is how they're decrypted during the session.
- Keeping your Master Password private & safe.
It's absolutely imperative to keep your master password safe. When you "sign in" (that's in quotes for reasons I'll explain later!) with LastPass/Dashlane, your master password never leaves your browser. It's not sent over the wire, not even on a supposedly-secure HTTPS connection... it remains private at all times. Your passwords and indeed all data is decrypted locally, on your device. This dramatically reduces the attack surface and helps ensure your data remains private.
Roboform also offer web-based access, but they go about it very differently. When you "sign in", your master password is sent to Roboform (Siber Systems), so your data is decrypted in the cloud. As Graham Cluley will tell you, "the cloud" is just "someone else's computer". It goes without saying, but the increased risk here is enormous.
Although Roboform insists they don't store your master password, merely having it is bad enough. If the transport layer is compromised (or simply not encrypted at all, such was the case a few months ago), your supposedly-private master password is now leaked to Roboform and anyone in between.
- Even genuine browser plugins can leak.
EditThisCookie is purely an example, but many plugins request similar permissions. Although the majority don't set out to steal your data, many leak it without realising.
Offline PW Managers
By minimising the attack surface, we can significantly reduce the risk.
If the entire process (encryption & decryption) is handled locally by your device, it's inherently safer than entering your credentials into an environment tainted by plugins and other threats.
Note: It's possible to leverage cloud-based synchronization while still decrypting locally. Assuming you've chosen a strong master password & the encryption is solid, there's no immediate risk in doing so.
If you re-use passwords, you're immediately exposed to multiple points of failure. With a secure PW manager and unique passwords, you should have a single point of failure... the master password.
Fallacies & Misconceptions
- 2FA
2FA in a password manager is not possible. Let me explain...
1. AES does not support 2FA!
For 2FA to be of any use, the encryption algorithm must require a second factor in order to decrypt your data and be impossible to decrypt without it. AES has no such facility. If you have the master password (rather the encryption key derived from it), you have everything necessary to decrypt the data.
Despite this obvious omission, some companies (LastPass, KeePass etc) still claim to offer 2FA to bolster security. More on that shortly.
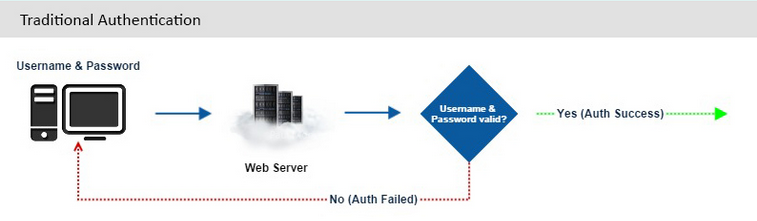
2. There is no authentication process, only decryption.
When you log in to a website, your username/email address & passwords are:
- Sent to the server.
- Checked against details stored in a database or similar.
The server is simply controlling access to the site with credentials you both have.
When you "sign in" to a password manager, you're not authenticating; it has no knowledge of your password and cannot simply compare the two.
3. Key splitting is not 2FA.
Some apps (KeePass etc) allow you to break your encryption key into two parts, one you remember, the other stored on a USB/Yubikey device.
The misconception here is that separating them into "something you know" and "something you have" somehow transforms this into 2FA. Keeping #2 in mind, could this be considered a two factor requirement rather than authentication?
No.
Remember, AES expects a key. You can break it into as many pieces as you like, it doesn't alter the requirements set out by AES. Key splitting helps mitigate the risks presented by malware (the "Citadel" keylogger, for example) but be under no illusion, the "second factor" still isn't a requirement, it's an option.
4. LastPass offers 2FA!
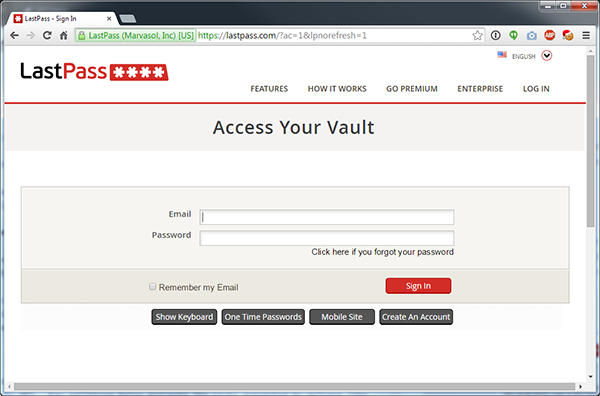
As we've already established, this isn't technically possible. To understand what's going on, let's look at the "sign in" screen.
At this point, you'd be forgiven for thinking the email address & password are sent to LastPass to be checked, but that's not true. Although the email address is sent, your "master password" remains in the browser and is never sent to LastPass.
Remember, this isn't data-level authentication... so despite entering "something you know" (password), this isn't even 1FA. This process controls access to the site, not the data directly.
Then, we reach the "multi-factor" screen.
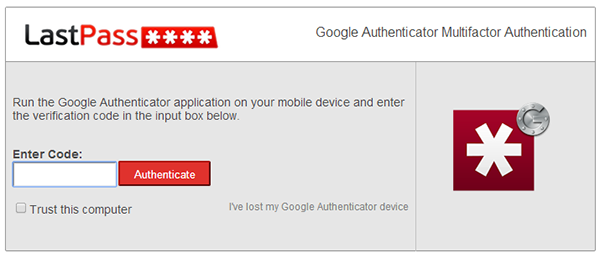
This is an authentication step, but it's the first one... making this 1FA. Keep in mind, someone with the encryption key can still decrypt your data, regardless of this process.
You could add a further step (2SV) or factor (2FA) here, but you're adding constraints to who can access the site, not how the data is decrypted.
Fear, Uncertainty & Doubt
- "I don't trust any 3rd-party app with my passwords"
I've never quite understood this logic.
Your browser is a 3rd-party app into which you willingly enter your credentials; some even saving them despite the fact they're often stored in plain text or easily reversed.
- "What about malware? Wouldn't 2FA protect against that?"
If I had a fiver for every citadel-related email, I'd retire a happy man.
As we've already established, 2FA isn't applicable in this context. If your KeePass (for example) data is stored on a machine compromised by malware like Citadel, it can log your keystrokes and potentially (although it doesn't just yet) access your data.
You can add as many faux-2FA steps as you like, you're only slowing yourself down.
- "If the company is hacked, you still lose your passwords!"
You'd lose one password, as they're all unique.
You'll still need to reset the compromised password, but it won't affect your other accounts unless it happens to be your email provider.
Revocation
Your email address is likely to be the common denominator between all your online accounts, so choosing a secure email provider is equally critical.
If an attacker is able to access your email, all of the above pales into insignificance. If they run password reset, it doesn't matter how long, strong or unique your password is... it'll be changed in a matter of minutes.
Take TalkTalk as an example. Their email services don't support encryption; even webmail credentials are sent in plain text.
If you're given the option to use 2FA/2SV to login to your email, use it... or you risk being a statistic.
Summary
It's tough to strike a balance between security & convenience; rarely can you increase one without measurably degrading the other.
A PW manager is one possible exception. They're so convenient, they allow you to use incredibly strong passwords which would otherwise be virtually impossible to remember.
They're not without risks, but the benefits far outweigh them.