Update: 2:50PM 03/02/2015
Just minutes after this article went live, SagePay have once again removed the 56bit cipher. It is being actively monitored, so if it creeps back in, I'll update the article again.
As one of the largest payment service providers in the world, SagePay has over 50,000 customers and processes over 4 billion payments each year.
The website is festooned with security claims:
Payment security and fraud prevention are two of our top priorities
Thousands of businesses already entrust us with their security because we keep our customer's data secure
Our services are completely secure
SagePay - http://www.sagepay.co.uk/support/online-shoppers/about-sage-pay
There's even a certificate to prove it:
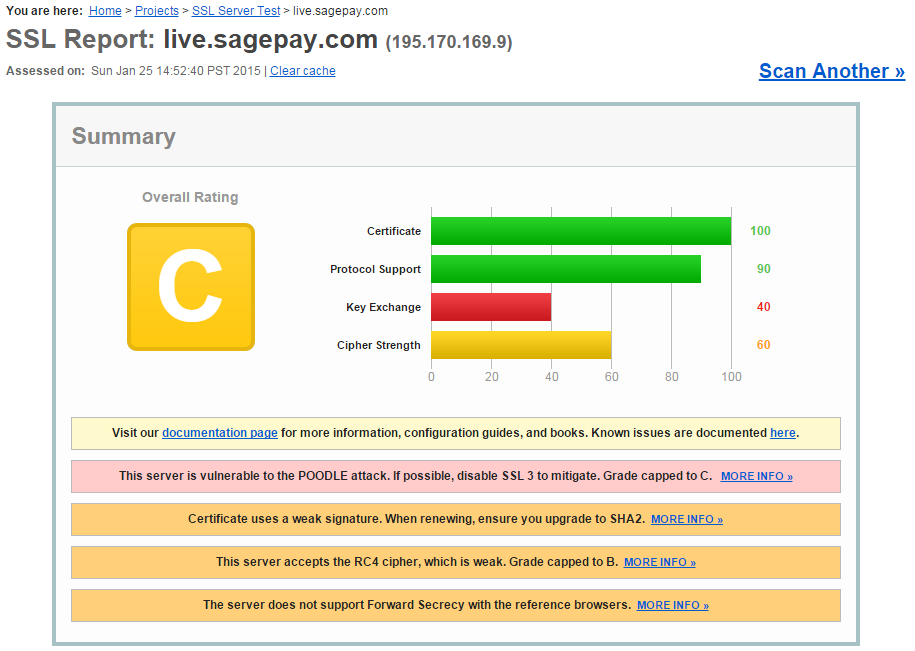
While investigating another serious security breach at "Office", a shoe retailer in London, I decided to run their PSP through the simplest of tests.
At first glance, it appears the POODLE/SSLv3 exploit is the most dangerous flaw... but that's not necessarily the case here.
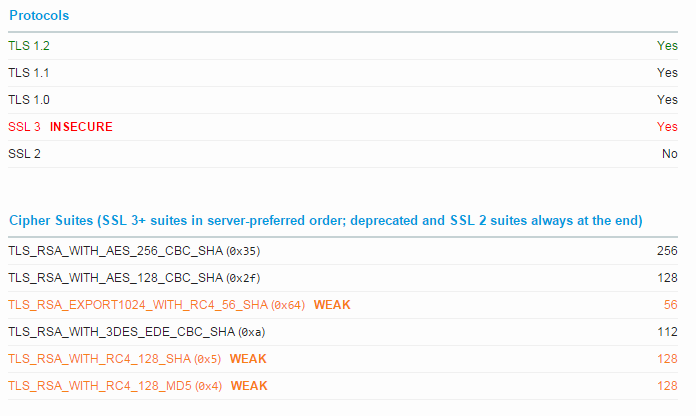
A 56bit export cipher?! That's not PCI compliant... it's not even close!
I tweeted SagePay on January 19th 2015 and within hours, I had the (interim) Head of Security on the phone to discuss it.
By the 22nd of January, the 56bit cipher had been removed and SagePay were (notwithstanding POODLE) PCI compliant.
If they've fixed it, what's the problem?
Well, just a few days later... the 56bit cipher returned!
On the 25th, I sent another message to the Head of Security asking why it had returned. Although I can't share the exact reason why, I can say that it was entirely intentional.
I must be honest, I was disgusted to discover their lack of compliance, but the speedy response did help alleviate my concerns. However, the fact they've knowingly reverted back demonstrates that quite apart from being a "top priority", security doesn't appear to be particularly important to them.
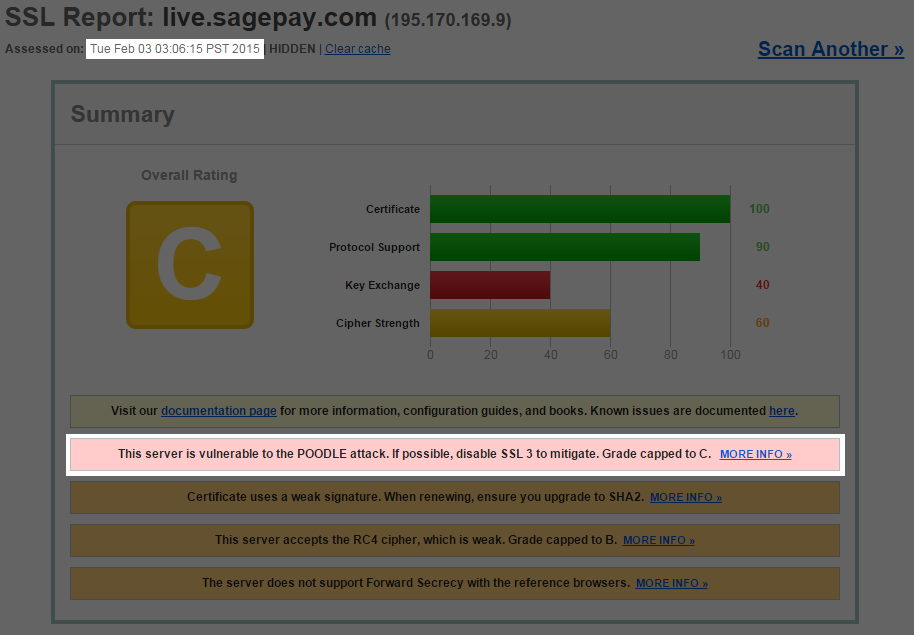
It's now February 3rd and it's still not compliant...
https://www.ssllabs.com/ssltest/analyze.html?d=live.sagepay.com
What about POODLE?
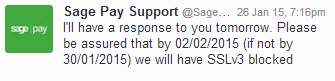
Responsible firms patched out POODLE months ago. SagePay are still lagging behind, so I raised the issue again on Twitter DM.
Drum roll...
Summary
As a result of these issues, I'm working to move several companies & local government accounts away from SagePay. If you value the security of your customer payment data, I'd advise you do the same.
Don't forget to +1, retweet and share folks.