05/01/2015:
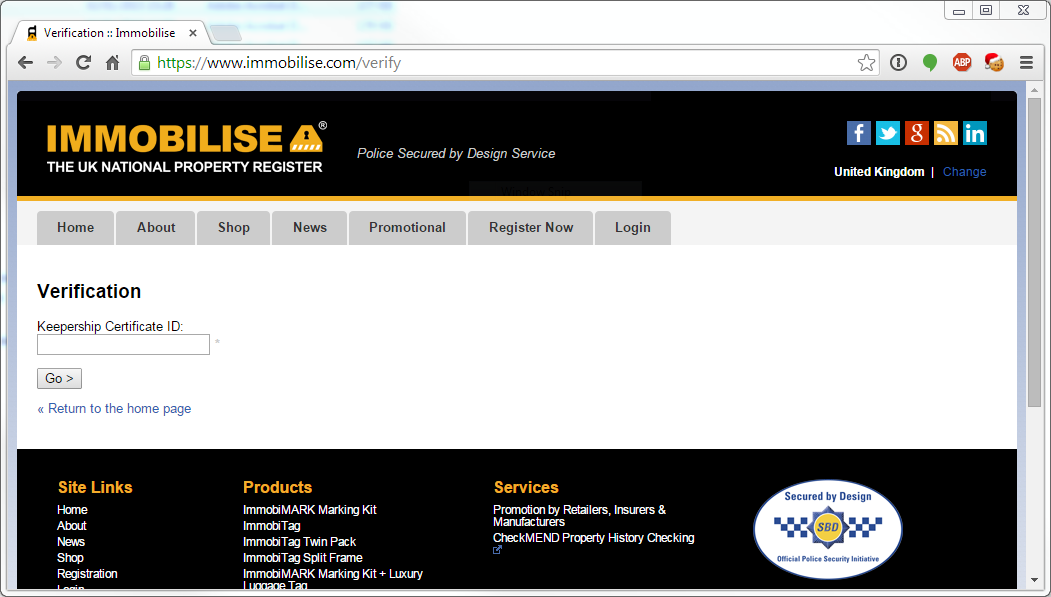
Recipero, the company behind Immobilise, NMPR and CheckMEND have now mitigated this risk by limiting access to the "/verify" & pdf generation pages to only authorized users. You're no longer able to view records which you do not own, so although it's undoubtedly more secure, the inability to verify the authenticity of a certificate appears to render this process pointless.
This exploit is known as a direct object reference, though I colloquially refer to it as the "open DOR" attack to signify the ease at which it can be detected & exploited. Immobilise isn't the first site to be vulnerable to such an attack, but it's first I've seen which appears to be built around this flawed principle. If this technique meets "secured by design" criteria, you have to question how reliable this (or indeed any) trustmark really is.
The POODLE/SSLv3 exploit at both NMPR and CheckMEND has also been resolved, with both scoring a healthy "A" at Qualys. Perhaps ironically, some forces are now unable to access the site because Internet Explorer (as shipped with Windows XP) is only able to use insecure protocols (SSLv3). It's now the responsibility of the affected forces to ensure their software meets current standards.

"Immobilise can be used by members of the public and businesses to register their valued possessions or company assets, and exclusive to Immobilise all account holders registered items and ownership details are viewable on the Police national property database the NMPR. https://www.immobilise.com"
With an estimated 4.2 million users and 28 million records, the UK's National Property Register is the largest site of its kind; supported by central government, the mobile phone industry and every police force in the UK.
Unfortunately, it's also a veritable goldmine for burglars.
Quite apart from being "secured by design", Immobilise is quite happy to hand over its information to anyone, if you ask nicely.
How does it work?
Christmas is over and you're stuffed to the gills with turkey. What better way to relax than sit in front of your new 50" 3D TV and watch Moonraker, again.
But, you're back to work next week and your precious TV will be left unattended at home. If it's stolen, reporting the theft to Immobilise can increase the likelihood of its safe return. Once you've registered your device, you're given a certificate of ownership.
To download your certificate, you're given a link which looks something like this.
https://www.immobilise.com/pdf.php?stage=account&certificate=7161519&user=3714932
How is it vulnerable?
To understand what's going on, let's take a closer look at the certificate.
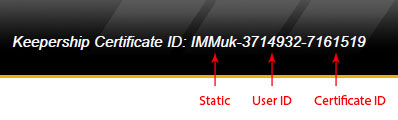
An attacker wouldn't know the "User ID" or "Certificate ID", so it's safe, right?
Far from it! The numbers aren't random, they're sequential, thus deterministic. If the last certificate number is 7161519, the next is 7161520 and so on. However, if someone happens to add another item to their account before you, your next number is 7161521.
By simply looping through every combination, it's possible to collect all 28+ million entries.
That's quite a nice shopping list for a would-be burglar! They'll know your name, home address, telephone number(s), email address, the make/model of your item, any identifying factors (serial numbers, IMEIs, unique marks etc) and even how much it's worth! Sure, it'll take some time and you're bound to hit a rate limiter along the way, but even if it takes a day/week/month, it's worth the wait.
Like you, I presumed this was a vulnerability and followed the usual responsible disclosure procedures. I sent this issue, along with several others to Les Gray (COO @ Recipero) in 2013. The most critical issues were patched very quickly; Les couldn't have been more helpful.
However, this particular issue still remains. In the last 48hrs, I realised this was actually intentional!
If you hand over a certificate to the police or your insurance company, they can use this page to confirm its authenticity.
What should I do?
Report it to the Information Commissioner's Office and delete your account immediately.
Had this been a simple vulnerability, that'd probably be overkill (though justified). As it's "by design" and mindful of the other issues which I can't disclose... the benefits just don't outweigh the risks.
I recently joined Immobilise and I've been burgled, is this to blame?
It's possible, but very doubtful.
Is the data secure once it reaches the Police?
Immobilise is the public-facing area of the system, so it's quite easy to carry out some basic checks.
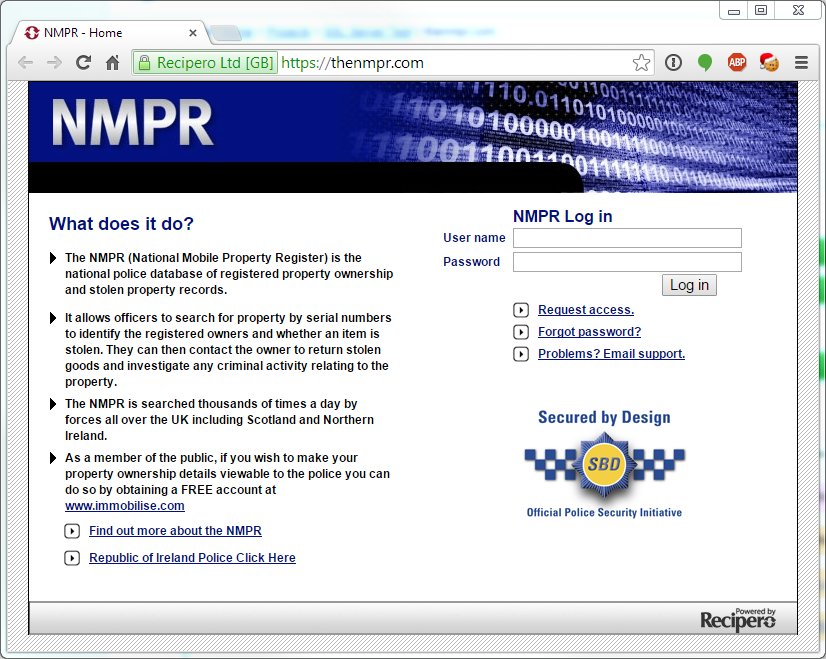
The NMPR (National Mobile Property Register) is the Police National database for stolen property, directly fed by Immobilise data.
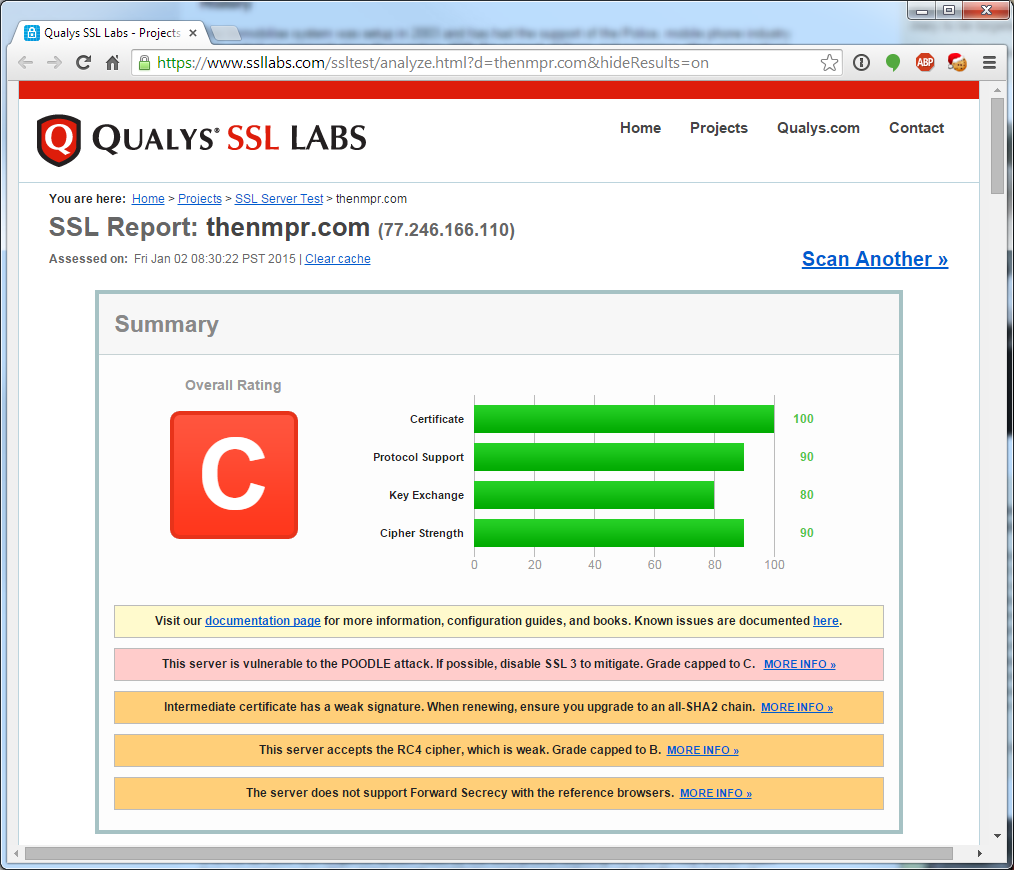
Unfortunately, they haven't bothered patching out POODLE/SSLv3...
Mindful of the government's propensity for using Windows XP and other archaic technology, it's entirely possible their credentials are travelling over the transport layer using insecure encryption. This system (and the sister site, CheckMEND) contain over 150 billion records. No, that's not a typo.
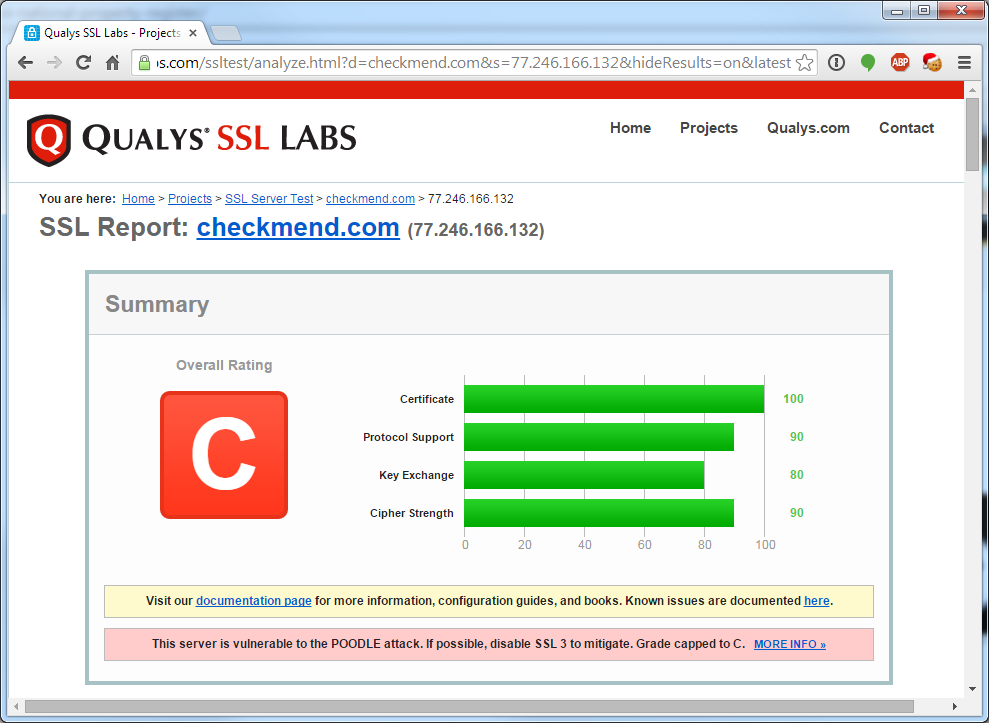
In case you're wondering, CheckMEND is also vulnerable to POODLE/SSLv3.
Summary
This is sadly one of those occasions when there's very little you can do to protect yourself. It uses HTTPS, it's backed by every UK police force and sports a plethora of padlocks & security trustmarks; there's no outward sign whatsoever that you're about to put your home at risk.
The moral of this story is two-fold.
- Always be careful of what information you share on the web.
and - Take trustmarks, padlocks and privacy policies with a pinch of salt. Even something which looks secure can be wide open to abuse.